- 7668 Goodwood Blvd, Baton Rouge, LA 70806
Network Data Risk Management
Gulf South Technology Solutions Reduces Your Risk and Keeps Your Business Compliant.
assess and mitigate security risks across your entire organization
We identify, classify, monitor and mitigate the risks of your network.




Businesses today rely heavily on the use of technology, and with this reliance comes an increased security risk. With most of our business documents, transactions, and communications being handled almost exclusively on computers and networks, the need for security and risk management services is vital.
Gulf South Technology Solutions understands that IT risk management is not a “one size fits all” solution. We understand that risk management is an ongoing process and work with your organization to continuously assess risks and establish security objectives so that solutions can be implemented specifically for your business.
Identify your Risks
Risk Assessment Report
Every business that relies on technology faces some sort of risk as they do business.
Gulf South Technology Solutions can help you identify these risks, prioritize them and let you see which items need to be acted on.
When we work with an organization, we develop a detailed risk report that identifies potential security risks specific to that organization’s systems and networks.
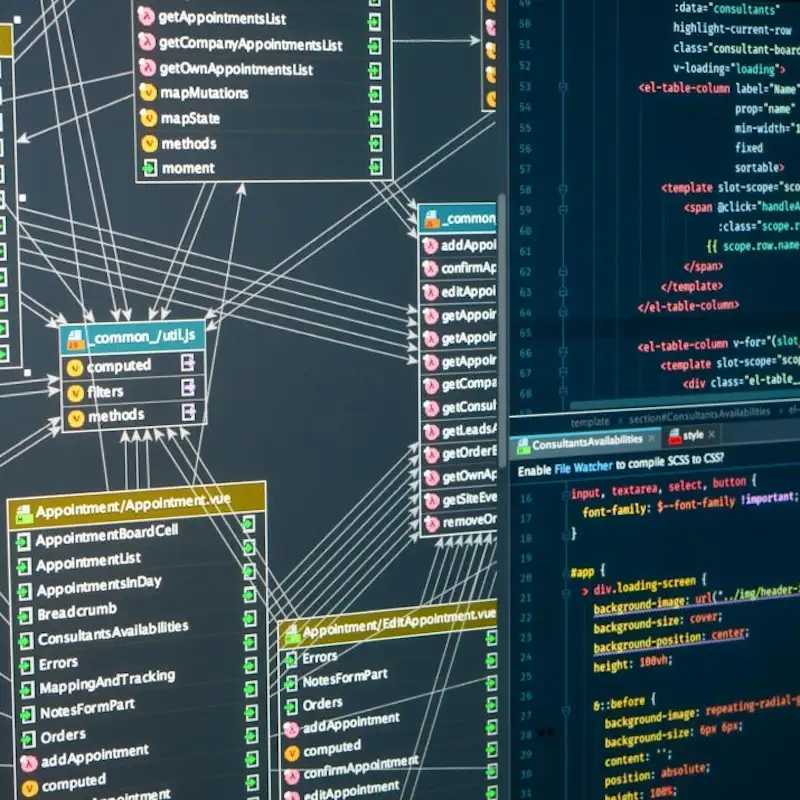
Risk Discovery and Score
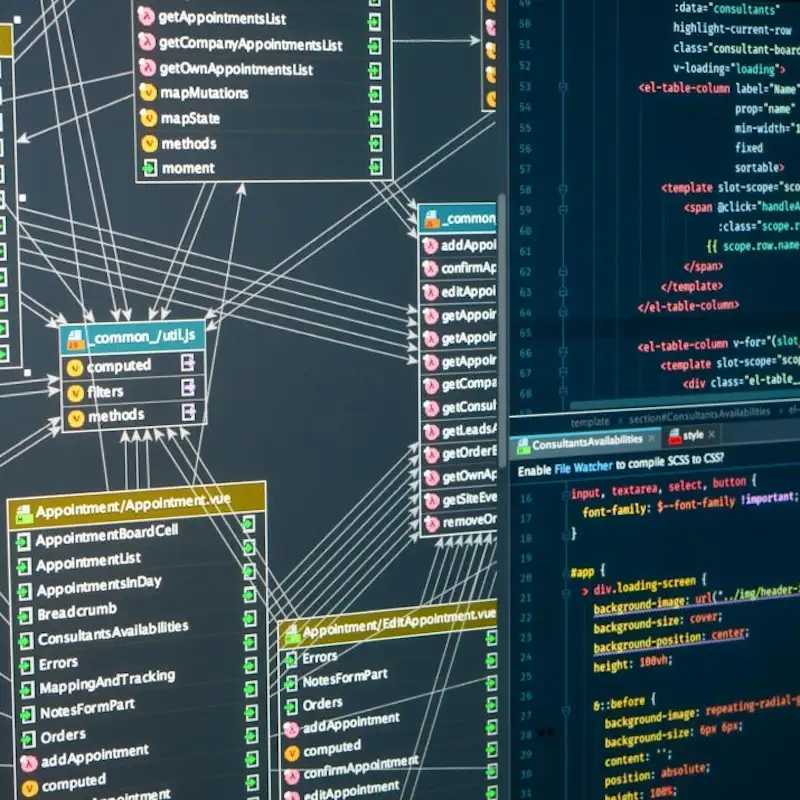
Our risk report includes a detailed discovery process, which allows us to analyze the entirety of an organization’s systems and provides a detailed list of items of concern.
Once the reports have been run, we provide a Risk Score, which ranges from Low to High Risk, with a detailed list of issues that need to be investigated in more detail and addressed as needed.


Detailed Asset and Resource Listings
In addition to our overall risk assessment and score, our report provides us with a detailed overview of your systems including:
- Internet download/upload speeds
- Hardware Overview including: Computers, operating systems, servers, printers, etc
- Total number of users (both active and inactive)
- User Security Distribution (access and account levels)
- Detailed storage drive capacity and usage reports
This additional information allows Gulf South Technology Solutions to present you with a complete look at your systems. We can then inform you of outdated or insecure hardware and software, and let you know what your overall recovery time from crash to restoration would be with your existing systems and backup solutions.

